Key agreement protocol
Key agreement protocol - Search results - Wiki Key Agreement Protocol
The page "Key+agreement+protocol" does not exist. You can create a draft and submit it for review or request that a redirect be created, but consider checking the search results below to see whether the topic is already covered.
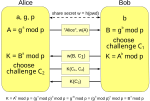
- In cryptography, a key-agreement protocol is a protocol whereby two or more parties can agree on a cryptographic key in such a way that both influence...
 key exchange is a mathematical method of securely exchanging cryptographic keys over a public channel and was one of the first public-key protocols as...
key exchange is a mathematical method of securely exchanging cryptographic keys over a public channel and was one of the first public-key protocols as...- password-authenticated key agreement (PAK) method is an interactive method for two or more parties to establish cryptographic keys based on one or more...
- Elliptic-curve Diffie–Hellman (category Key-agreement protocols)Diffie–Hellman (ECDH) is a key agreement protocol that allows two parties, each having an elliptic-curve public–private key pair, to establish a shared...
 (IBE) Key escrow Key-agreement protocol PGP word list Post-quantum cryptography Pretty Good Privacy Pseudonym Public key fingerprint Public key infrastructure...
(IBE) Key escrow Key-agreement protocol PGP word list Post-quantum cryptography Pretty Good Privacy Pseudonym Public key fingerprint Public key infrastructure...- ZRTP (redirect from Z Real-time Transport Protocol)(composed of Z and Real-time Transport Protocol) is a cryptographic key-agreement protocol to negotiate the keys for encryption between two end points...
- Internet Key Exchange (IKE, versioned as IKEv1 and IKEv2) is the protocol used to set up a security association (SA) in the IPsec protocol suite. IKE...
- In public-key cryptography, the Station-to-Station (STS) protocol is a cryptographic key agreement scheme. The protocol is based on classic Diffie–Hellman...
- The Secure Remote Password protocol (SRP) is an augmented password-authenticated key exchange (PAKE) protocol, specifically designed to work around existing...
- Simultaneous Authentication of Equals (category Key-agreement protocols)knowing the user's password." Extensible Authentication Protocol (EAP) Key-agreement protocol KRACK IEEE 802.1X Harkins, Dan (Aug 20, 2008). "Simultaneous...
- Authentication and Key Agreement (AKA) is a security protocol used in 3G networks. AKA is also used for one-time password generation mechanism for digest...
- Skype security (section Key agreement protocol)public keys are certified by the Skype server at login with 1536-bit or 2048-bit RSA certificates. Skype's encryption is inherent in the Skype Protocol and...
- MQV (category Key-agreement protocols)MQV (Menezes–Qu–Vanstone) is an authenticated protocol for key agreement based on the Diffie–Hellman scheme. Like other authenticated Diffie–Hellman schemes...
 Signal (messaging app) (section Encryption protocols)2017, Signal's voice calls were encrypted with SRTP and the ZRTP key-agreement protocol, which was developed by Phil Zimmermann. In March 2017, Signal transitioned...
Signal (messaging app) (section Encryption protocols)2017, Signal's voice calls were encrypted with SRTP and the ZRTP key-agreement protocol, which was developed by Phil Zimmermann. In March 2017, Signal transitioned...- Authenticated Key Exchange by Juggling (or J-PAKE) is a password-authenticated key agreement protocol, proposed by Feng Hao and Peter Ryan. This protocol allows...
- Algebraic Eraser (category Key-agreement protocols)Algebraic Eraser (AE) is an anonymous key agreement protocol that allows two parties, each having an AE public–private key pair, to establish a shared secret...
 Encrypted Key Exchange (also known as EKE) is a family of password-authenticated key agreement methods described by Steven M. Bellovin and Michael Merritt...
Encrypted Key Exchange (also known as EKE) is a family of password-authenticated key agreement methods described by Steven M. Bellovin and Michael Merritt...- protocols as well, and even the term itself has various readings; Cryptographic application protocols often use one or more underlying key agreement methods...
- information (such as public keys) in addition to the message over a secure channel. Such protocols, often using key-agreement protocols, have been developed...
- Accordingly, key authentication methods are being actively researched. Public-key infrastructure (PKI) Public-key cryptography Key-agreement protocol Access...
- 1911 Encyclopædia Britannica, Volume 22 Protocol 21713021911 Encyclopædia Britannica, Volume 22 — Protocol PROTOCOL (Fr. protocole, Late Lat. protocollum
- The Protocols of the Meetings of the Learned Elders of Zion is a fabricated antisemitic text purporting to describe a grand design of Zionist movement
- secret hiding better or more convenient in some way -- key-agreement protocols such as Diffie-Hellman key exchange Message authentication (FIXME: say something