Block Cipher Mode Of Operation Padding
Block Cipher Mode Of Operation Padding - Search results - Wiki Block Cipher Mode Of Operation Padding
The page "Block+Cipher+Mode+Of+Operation+Padding" does not exist. You can create a draft and submit it for review or request that a redirect be created, but consider checking the search results below to see whether the topic is already covered.
 In cryptography, a block cipher mode of operation is an algorithm that uses a block cipher to provide information security such as confidentiality or...
In cryptography, a block cipher mode of operation is an algorithm that uses a block cipher to provide information security such as confidentiality or...- cryptography, a block cipher is a deterministic algorithm that operates on fixed-length groups of bits, called blocks. Block ciphers are the elementary...
- In cryptography, Galois/Counter Mode (GCM) is a mode of operation for symmetric-key cryptographic block ciphers which is widely adopted for its performance...
- CCM mode (counter with cipher block chaining message authentication code; counter with CBC-MAC) is a mode of operation for cryptographic block ciphers. It...
- EAX mode (encrypt-then-authenticate-then-translate) is a mode of operation for cryptographic block ciphers. It is an Authenticated Encryption with Associated...
- Offset codebook mode (OCB mode) is an authenticated encryption mode of operation for cryptographic block ciphers. OCB mode was designed by Phillip Rogaway...
- key block cipher with a block size of 128 bits and key sizes of 128, 192 and 256 bits. It was jointly developed by Mitsubishi Electric and NTT of Japan...
- SHA-512/224, and SHA-512/256 Cipher-block chaining (CBC) mode is an example of block cipher mode of operation. Some block cipher modes (CBC and PCBC essentially)...
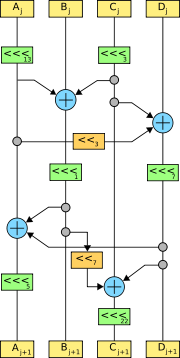
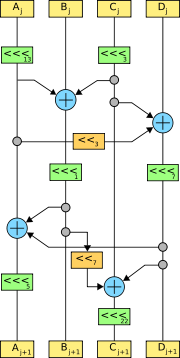
- cryptography, a Feistel cipher (also known as Luby–Rackoff block cipher) is a symmetric structure used in the construction of block ciphers, named after the...
- Initialization vector (category Block cipher modes of operation)segments of the encrypted message. For block ciphers, the use of an IV is described by the modes of operation. Some cryptographic primitives require the...
 clear-cut: in some modes of operation, a block cipher primitive is used in such a way that it acts effectively as a stream cipher. Stream ciphers typically execute...
clear-cut: in some modes of operation, a block cipher primitive is used in such a way that it acts effectively as a stream cipher. Stream ciphers typically execute...- after Serge Vaudenay's attack on the CBC mode decryption used within symmetric block ciphers. Variants of both attacks continue to find success more...
- In cryptography, the Iraqi block cipher was a block cipher published in C source code form by anonymous FTP upload around July 1999, and widely distributed...
- Authenticated encryption (redirect from AEAD block cipher modes of operation)confidentiality and authentication block cipher operation modes could be error prone and difficult. This was confirmed by a number of practical attacks introduced...
- In cryptography, CWC Mode (Carter–Wegman + CTR mode) is an AEAD block cipher mode of operation that provides both encryption and built-in message integrity...
- parallelizable mode (IAPM) is a mode of operation for cryptographic block ciphers. As its name implies, it allows for a parallel mode of operation for higher...
- Intel Cascaded Cipher is a high bandwidth block cipher, used as an optional component of the Output Content Protection DRM scheme of the Microsoft Windows...
 Xor–encrypt–xor (redirect from Even-Mansour cipher)mode of operation of a block cipher. In tweaked-codebook mode with ciphertext stealing (XTS mode), it is one of the more popular modes of operation for...
Xor–encrypt–xor (redirect from Even-Mansour cipher)mode of operation of a block cipher. In tweaked-codebook mode with ciphertext stealing (XTS mode), it is one of the more popular modes of operation for...- Blowfish is a symmetric-key block cipher, designed in 1993 by Bruce Schneier and included in many cipher suites and encryption products. Blowfish provides...
 Serpent is a symmetric key block cipher that was a finalist in the Advanced Encryption Standard (AES) contest, in which it ranked second to Rijndael. Serpent...
Serpent is a symmetric key block cipher that was a finalist in the Advanced Encryption Standard (AES) contest, in which it ranked second to Rijndael. Serpent...
- mere ciphers, now teach it through the evidence of the senses in the manner we have described." Here we may, I think, trace the solitary source of weakness
- using AES-256, there's no reason to change." "Which is the Best Cipher Mode and Padding Mode for AES Encryption?". Ignat Korchagin. "Speeding up Linux disk