Block Cipher Mode Of Operation Initialization vector (IV)
Block Cipher Mode Of Operation Initialization vector (IV) - Search results - Wiki Iv Block Cipher Mode Of Operation Initialization Vector
The page "Block+Cipher+Mode+Of+Operation+Initialization+vector+(IV)" does not exist. You can create a draft and submit it for review or request that a redirect be created, but consider checking the search results below to see whether the topic is already covered.
 than a block. Most modes require a unique binary sequence, often called an initialization vector (IV), for each encryption operation. The IV must be...
than a block. Most modes require a unique binary sequence, often called an initialization vector (IV), for each encryption operation. The IV must be...- cryptography, an initialization vector (IV) or starting variable is an input to a cryptographic primitive being used to provide the initial state. The IV is typically...
- In cryptography, Galois/Counter Mode (GCM) is a mode of operation for symmetric-key cryptographic block ciphers which is widely adopted for its performance...
- CCM mode (counter with cipher block chaining message authentication code; counter with CBC-MAC) is a mode of operation for cryptographic block ciphers. It...
 clear-cut: in some modes of operation, a block cipher primitive is used in such a way that it acts effectively as a stream cipher. Stream ciphers typically execute...
clear-cut: in some modes of operation, a block cipher primitive is used in such a way that it acts effectively as a stream cipher. Stream ciphers typically execute...- Authenticated encryption (redirect from AEAD block cipher modes of operation)confidentiality and authentication block cipher operation modes could be error prone and difficult. This was confirmed by a number of practical attacks introduced...
- r {\displaystyle c=320-r} . The state is initialized by an initialization vector IV (constant for each cipher type, e.g., hex 80400c0600000000 for Ascon-128)...
- Disk encryption theory (redirect from LRW mode)ESSIV approach uses a block cipher in CTR mode to generate the IVs. ESSIV is a method for generating initialization vectors for block encryption to use in...
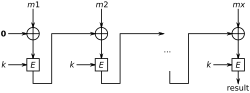
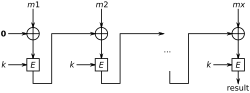 CBC-MAC (category Block cipher modes of operation)to the block cipher. To calculate the CBC-MAC of message m, one encrypts m in CBC mode with zero initialization vector and keeps the last block. The following...
CBC-MAC (category Block cipher modes of operation)to the block cipher. To calculate the CBC-MAC of message m, one encrypts m in CBC mode with zero initialization vector and keeps the last block. The following...- AES-GCM-SIV (category Block cipher modes of operation)AES-GCM-SIV is a mode of operation for the Advanced Encryption Standard which provides similar performance to Galois/Counter Mode as well as misuse resistance...
 Symmetric-key algorithm (redirect from Symmetric cipher)use either stream ciphers or block ciphers. Stream ciphers encrypt the digits (typically bytes), or letters (in substitution ciphers) of a message one at...
Symmetric-key algorithm (redirect from Symmetric cipher)use either stream ciphers or block ciphers. Stream ciphers encrypt the digits (typically bytes), or letters (in substitution ciphers) of a message one at...- Transport Layer Security (redirect from Security of Transport Layer Security)against cipher-block chaining (CBC) attacks. The implicit initialization vector (IV) was replaced with an explicit IV. Change in handling of padding errors...
- BLAKE (hash function) (section Initialization vector)function based on Daniel J. Bernstein's ChaCha stream cipher, but a permuted copy of the input block, XORed with round constants, is added before each ChaCha...
- general method of using a block cipher mode of operation that allows for processing of messages that are not evenly divisible into blocks without resulting...
- RC4 (redirect from RC4 Cipher)the way cipher-block chaining mode is used with all of the other ciphers supported by TLS 1.0, which are all block ciphers. In March 2013, there were new...
- use an initialization vector (IV), sent in the clear, that is combined with a secret master key to create a one-time key for the stream cipher. This is...
- EncFS (section Per-file IV initialization vector)this mode is enabled requires that either the file's random initialization vector be offset by the change in the filename initialization vector chain...
- after Serge Vaudenay's attack on the CBC mode decryption used within symmetric block ciphers. Variants of both attacks continue to find success more...
- Another mode, Cipher Block Chaining (CBC) is one of the most commonly used modes of AES due to its use in TLS. CBC uses a random initialization vector (IV) to...
- initrd image itself. When using the cipher block chaining mode of operation with predictable initialization vectors as other disk encryption software,...
- or scalar quantities, not vectors, and they can have positive or negative values. However, in AC mode, the overall function of voltage with time V(t), can