Black And White Computing
Black And White Computing - Search results - Wiki Black And White Computing
The page "Black+And+White+Computing" does not exist. You can create a draft and submit it for review or request that a redirect be created, but consider checking the search results below to see whether the topic is already covered.
 in black and white. In computing terminology, black-and-white is sometimes used to refer to a binary image consisting solely of pure black pixels and pure...
in black and white. In computing terminology, black-and-white is sometimes used to refer to a binary image consisting solely of pure black pixels and pure... The black swan theory or theory of black swan events is a metaphor that describes an event that comes as a surprise, has a major effect, and is often inappropriately...
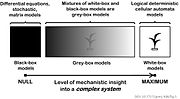
The black swan theory or theory of black swan events is a metaphor that describes an event that comes as a surprise, has a major effect, and is often inappropriately...- In science, computing, and engineering, a black box is a system which can be viewed in terms of its inputs and outputs (or transfer characteristics), without...
- comes from Western films, where heroic and antagonistic cowboys might traditionally wear a white and a black hat, respectively. There is a third kind...
 Light-on-dark color scheme (redirect from Blazing white (computing))appealing, and claim that it can reduce eye strain. Displaying white at full brightness uses roughly six times as much power as pure black on a 2016 Google...
Light-on-dark color scheme (redirect from Blazing white (computing))appealing, and claim that it can reduce eye strain. Displaying white at full brightness uses roughly six times as much power as pure black on a 2016 Google...- and with file extension .wbmp) is a monochrome graphics file format optimized for mobile computing devices. WBMP images are monochrome (black & white)...
 events in the history of computing from 1990 to 1999. For narratives explaining the overall developments, see the history of computing. "Redirecting to Google...
events in the history of computing from 1990 to 1999. For narratives explaining the overall developments, see the history of computing. "Redirecting to Google... The notion of a "Black Box in a Glass Box" was originally used as a metaphor for teaching complex topics to computing novices. Black box Gray-box testing...
The notion of a "Black Box in a Glass Box" was originally used as a metaphor for teaching complex topics to computing novices. Black box Gray-box testing...- traditional computing. A simple example considers images containing black circles and white squares. Hypervectors can represent SHAPE and COLOR variables and hold...
 A black hole is a region of spacetime where gravity is so strong that nothing, including light and other electromagnetic waves, is capable of possessing...
A black hole is a region of spacetime where gravity is so strong that nothing, including light and other electromagnetic waves, is capable of possessing... events in the history of computing from 2000 to 2009. For narratives explaining the overall developments, see the history of computing. Informational revolution...
events in the history of computing from 2000 to 2009. For narratives explaining the overall developments, see the history of computing. Informational revolution... CMYK color model (redirect from Cyan, Magenta, Yellow, and Key Color Model)white is the "additive" combination of all primary colored lights, and black is the absence of color. In the CMYK model, it is the opposite: white is...
CMYK color model (redirect from Cyan, Magenta, Yellow, and Key Color Model)white is the "additive" combination of all primary colored lights, and black is the absence of color. In the CMYK model, it is the opposite: white is...- Gender disparity in computing concerns the disparity between the number of men in the field of computing in relation to the lack of women in the field...
- Whitelist (redirect from White list)negative connotation behind "black" and "blacklist" both predate attribution to race. Blacklisting Blacklist (computing) Closed platform DNSWL, whitelisting...
- repeat. This practice generally refers to software vulnerabilities in computing systems. Agile vulnerability management refers to preventing attacks by...
 events in the history of computing from 1980 to 1989. For narratives explaining the overall developments, see the history of computing. "Behind a pizza-slice...
events in the history of computing from 1980 to 1989. For narratives explaining the overall developments, see the history of computing. "Behind a pizza-slice...- In computing, Xyzzy is sometimes used as a metasyntactic variable or as a video game cheat code. Xyzzy comes from the Colossal Cave Adventure computer...
- Trusted Computing (TC) is a technology developed and promoted by the Trusted Computing Group. The term is taken from the field of trusted systems and has...
- Green computing, green IT (Information Technology), or ICT sustainability, is the study and practice of environmentally sustainable computing or IT. The...
 In computing, a blacklist, disallowlist, blocklist, or denylist is a basic access control mechanism that allows through all elements (email addresses...
In computing, a blacklist, disallowlist, blocklist, or denylist is a basic access control mechanism that allows through all elements (email addresses...
- Black and White: Land, Labor, and Politics in the South (1884) by Timothy Thomas Fortune 3322069Black and White: Land, Labor, and Politics in the South1884Timothy
- how racism hurts white people. With the George Floyd protests and people's uprising, white folks are seeing, again, that what Black and brown folks have
- We have studied some fundamental principles of computing and seen the power of computing demonstrated in powerful technologies that operate on these principles