Open a Digital Safe Without a Key
Open a Digital Safe Without a Key - Search results - Wiki Open A Digital Safe Without A Key
The page "Open+a+Digital+Safe+Without+a+Key" does not exist. You can create a draft and submit it for review or request that a redirect be created, but consider checking the search results below to see whether the topic is already covered.
 Safe-cracking is the process of opening a safe without either the combination or the key. Safes have widely different designs, construction methods, and...
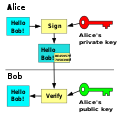
Safe-cracking is the process of opening a safe without either the combination or the key. Safes have widely different designs, construction methods, and... computationally infeasible to generate a valid signature for a party without knowing that party's private key. A digital signature is an authentication mechanism...
computationally infeasible to generate a valid signature for a party without knowing that party's private key. A digital signature is an authentication mechanism...- EdDSA (redirect from Edwards-Curve Digital Signature Algorithm)In public-key cryptography, Edwards-curve Digital Signature Algorithm (EdDSA) is a digital signature scheme using a variant of Schnorr signature based...
 public-key cryptography depends on keeping the private key secret; the public key can be openly distributed without compromising security. In a public-key encryption...
public-key cryptography depends on keeping the private key secret; the public key can be openly distributed without compromising security. In a public-key encryption...- Cryptocurrency wallet (category Digital currency exchanges)a safe physical location for later retrieval.: 39 Physical wallets can also take the form of metal token coins with a private key accessible under a...
- It can also be a computer containing an interlocking computer program with digital or analogue electronics. Trapped-key interlocking is a method of ensuring...
- Post-quantum cryptography (redirect from Quantum Safe Cryptography)quantum-safe, or quantum-resistant, is the development of cryptographic algorithms (usually public-key algorithms) that are thought to be secure against a cryptanalytic...
 (DH) key exchange is a mathematical method of securely exchanging cryptographic keys over a public channel and was one of the first public-key protocols...
(DH) key exchange is a mathematical method of securely exchanging cryptographic keys over a public channel and was one of the first public-key protocols...- Key management refers to management of cryptographic keys in a cryptosystem. This includes dealing with the generation, exchange, storage, use, crypto-shredding...
- VingCard Elsafe (section Elsafe safes)a security vault that opened and closed electronically, and new electronic safes soon led to an industry-wide shift, where safes requiring metal keys...
- Kyber (category Asymmetric-key algorithms)cryptographic operations. For a chat encryption scenario using liboqs, replacing the extremely efficient, non-quantum-safe ECDH key exchange using Curve25519...
 The Open Network (previously Telegram Open Network, both abb. as TON) is a decentralized computer network consisting of a layer-1 blockchain with various...
The Open Network (previously Telegram Open Network, both abb. as TON) is a decentralized computer network consisting of a layer-1 blockchain with various... Hardware security module (redirect from Hardware security key)A hardware security module (HSM) is a physical computing device that safeguards and manages secrets (most importantly digital keys), performs encryption...
Hardware security module (redirect from Hardware security key)A hardware security module (HSM) is a physical computing device that safeguards and manages secrets (most importantly digital keys), performs encryption... previous choice of a w-bit internal "key", and this guarantee holds as long as the strings r and s are chosen without knowledge of the key. Rabin's method...
previous choice of a w-bit internal "key", and this guarantee holds as long as the strings r and s are chosen without knowledge of the key. Rabin's method...- as well as full open-sourcing of Lightway's code. In 2020, ExpressVPN announced its new digital security research initiative Digital Security Lab, which...
 Key exchange (also key establishment) is a method in cryptography by which cryptographic keys are exchanged between two parties, allowing use of a cryptographic...
Key exchange (also key establishment) is a method in cryptography by which cryptographic keys are exchanged between two parties, allowing use of a cryptographic...- Elliptic-curve cryptography (category Public-key cryptography)for key agreement, digital signatures, pseudo-random generators and other tasks. Indirectly, they can be used for encryption by combining the key agreement...
- Certificate authority (category Public-key cryptography)cryptography, a certificate authority or certification authority (CA) is an entity that stores, signs, and issues digital certificates. A digital certificate...
 Digital marketing is the component of marketing that uses the Internet and online-based digital technologies such as desktop computers, mobile phones...
Digital marketing is the component of marketing that uses the Internet and online-based digital technologies such as desktop computers, mobile phones... could imagine doing was moving humanity closer to building real AI in a safe way." OpenAI co-founder Wojciech Zaremba stated that he turned down "borderline...
could imagine doing was moving humanity closer to building real AI in a safe way." OpenAI co-founder Wojciech Zaremba stated that he turned down "borderline...
- Scholar'. 'Digital' and 'open' are not necessarily synonymous of course – someone could create all their outputs in digital format but store them on a local
- networks. Today’s children and teens do not know a world without digital technology, but the digital world wasn’t built with children’s healthy mental
- greatly simplified. Public key encryption is used for internet secure links, such as when a browser opens a bank site or a site used with credit cards